What Type Of Attack Exploits A Lack Of Bounds Checking On The Size Of Data Stored In An Array?

Visualization of a software buffer overflow. Data is written into A, just is likewise large to fit within A, so it overflows into B.
In information security and programming, a buffer overflow, or buffer overrun, is an anomaly where a program, while writing data to a buffer, overruns the buffer's boundary and overwrites adjacent retention locations.
Buffers are areas of retention set aside to agree data, often while moving it from one department of a programme to another, or between programs. Buffer overflows can often exist triggered by malformed inputs; if 1 assumes all inputs will exist smaller than a certain size and the buffer is created to exist that size, then an anomalous transaction that produces more information could cause information technology to write past the end of the buffer. If this overwrites adjacent data or executable code, this may result in erratic plan behavior, including memory access errors, incorrect results, and crashes.
Exploiting the behavior of a buffer overflow is a well-known security exploit. On many systems, the memory layout of a program, or the system equally a whole, is well defined. Past sending in data designed to cause a buffer overflow, it is possible to write into areas known to hold executable code and replace it with malicious lawmaking, or to selectively overwrite data pertaining to the program's state, therefore causing behavior that was non intended past the original programmer. Buffers are widespread in operating system (OS) lawmaking, then it is possible to make attacks that perform privilege escalation and proceeds unlimited access to the figurer'south resource. The famed Morris worm in 1988 used this every bit one of its assault techniques.
Programming languages usually associated with buffer overflows include C and C++, which provide no built-in protection confronting accessing or overwriting data in any role of memory and do not automatically check that information written to an array (the built-in buffer blazon) is within the boundaries of that array. Bounds checking tin can forestall buffer overflows, but requires additional code and processing time. Modern operating systems use a variety of techniques to gainsay malicious buffer overflows, notably by randomizing the layout of memory, or deliberately leaving space between buffers and looking for actions that write into those areas ("canaries").
Technical description [edit]
A buffer overflow occurs when data written to a buffer also corrupts data values in memory addresses adjacent to the destination buffer due to insufficient premises checking. This can occur when copying data from one buffer to another without first checking that the data fits inside the destination buffer.
Case [edit]
In the post-obit example expressed in C, a program has two variables which are next in retentivity: an 8-byte-long string buffer, A, and a two-byte large-endian integer, B.
char A [ 8 ] = "" ; unsigned short B = 1979 ; Initially, A contains nix but zero bytes, and B contains the number 1979.
| variable name | A | B | ||||||||
|---|---|---|---|---|---|---|---|---|---|---|
| value | [nothing cord] | 1979 | ||||||||
| hex value | 00 | 00 | 00 | 00 | 00 | 00 | 00 | 00 | 07 | BB |
Now, the program attempts to store the null-terminated string "excessive" with ASCII encoding in the A buffer.
"excessive" is 9 characters long and encodes to 10 bytes including the null terminator, but A tin can have only 8 bytes. By failing to check the length of the string, information technology also overwrites the value of B:
| variable proper name | A | B | ||||||||
|---|---|---|---|---|---|---|---|---|---|---|
| value | 'eastward' | 'x' | 'c' | 'eastward' | 's' | 's' | 'i' | 'v' | 25856 | |
| hex | 65 | 78 | 63 | 65 | 73 | 73 | 69 | 76 | 65 | 00 |
B's value has now been inadvertently replaced past a number formed from office of the graphic symbol string. In this example "eastward" followed by a nada byte would become 25856.
Writing data past the end of allocated retentiveness can sometimes be detected by the operating system to generate a segmentation mistake error that terminates the process.
To preclude the buffer overflow from happening in this instance, the call to strcpy could be replaced with strlcpy, which takes the maximum capacity of A (including a zippo-termination grapheme) as an additional parameter and ensures that no more than than this amount of information is written to A:
strlcpy ( A , "excessive" , sizeof ( A )); When available, the strlcpy library function is preferred over strncpy which does not nada-cease the destination buffer if the source string's length is greater than or equal to the size of the buffer (the third argument passed to the function), therefore A may non be nix-terminated and cannot be treated every bit a valid C-way string.
Exploitation [edit]
The techniques to exploit a buffer overflow vulnerability vary by architecture, by operating system and past memory region. For example, exploitation on the heap (used for dynamically allocated memory), differs markedly from exploitation on the call stack.
Stack-based exploitation [edit]
A technically inclined user may exploit stack-based buffer overflows to manipulate the plan to their advantage in one of several means:
- Past overwriting a local variable that is located near the vulnerable buffer on the stack, in gild to change the behavior of the program
- Past overwriting the return accost in a stack frame to indicate to code selected by the attacker, usually called the shellcode. In one case the function returns, execution will resume at the attacker's shellcode.
- Past overwriting a function pointer[1] or exception handler to point to the shellcode, which is subsequently executed
- By overwriting a local variable (or pointer) of a unlike stack frame, which will exist used by the part which owns that frame afterward.[2]
The attacker designs data to cause one of these exploits, then places this data in a buffer supplied to users by the vulnerable code. If the address of the user-supplied data used to affect the stack buffer overflow is unpredictable, exploiting a stack buffer overflow to cause remote code execution becomes much more than hard. One technique that can be used to exploit such a buffer overflow is called "trampolining". In that technique, an attacker will detect a pointer to the vulnerable stack buffer, and compute the location of their shellcode relative to that pointer. And so, they will use the overwrite to leap to an education already in memory which volition make a 2d leap, this fourth dimension relative to the pointer; that second jump will branch execution into the shellcode. Suitable instructions are often present in big code. The Metasploit Project, for example, maintains a database of suitable opcodes, though information technology lists merely those found in the Windows operating organization.[3]
Heap-based exploitation [edit]
A buffer overflow occurring in the heap information area is referred to equally a heap overflow and is exploitable in a manner dissimilar from that of stack-based overflows. Memory on the heap is dynamically allocated by the application at run-time and typically contains program data. Exploitation is performed past corrupting this information in specific ways to crusade the application to overwrite internal structures such equally linked listing pointers. The canonical heap overflow technique overwrites dynamic memory allocation linkage (such as malloc meta data) and uses the resulting pointer exchange to overwrite a program function arrow.
Microsoft's GDI+ vulnerability in handling JPEGs is an example of the danger a heap overflow tin present.[four]
Barriers to exploitation [edit]
Manipulation of the buffer, which occurs before it is read or executed, may lead to the failure of an exploitation attempt. These manipulations tin mitigate the threat of exploitation, but may not get in impossible. Manipulations could include conversion to upper or lower case, removal of metacharacters and filtering out of non-alphanumeric strings. However, techniques exist to bypass these filters and manipulations; alphanumeric shellcode, polymorphic code, self-modifying code and return-to-libc attacks. The same methods tin can be used to avoid detection by intrusion detection systems. In some cases, including where code is converted into Unicode,[five] the threat of the vulnerability has been misrepresented by the disclosers as just Denial of Service when in fact the remote execution of arbitrary code is possible.
Practicalities of exploitation [edit]
In real-world exploits there are a diverseness of challenges which need to be overcome for exploits to operate reliably. These factors include zero bytes in addresses, variability in the location of shellcode, differences between environments and diverse counter-measures in performance.
NOP sled technique [edit]
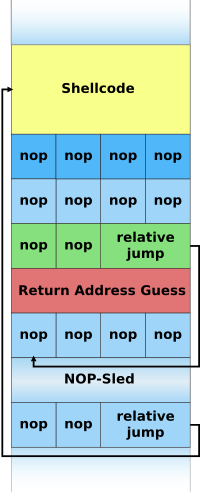
Illustration of a NOP-sled payload on the stack.
A NOP-sled is the oldest and most widely known technique for exploiting stack buffer overflows.[half-dozen] Information technology solves the problem of finding the exact accost of the buffer by effectively increasing the size of the target expanse. To practise this, much larger sections of the stack are corrupted with the no-op machine teaching. At the stop of the attacker-supplied data, later the no-op instructions, the aggressor places an didactics to perform a relative jump to the top of the buffer where the shellcode is located. This drove of no-ops is referred to as the "NOP-sled" considering if the return address is overwritten with any address within the no-op region of the buffer, the execution will "slide" downwardly the no-ops until it is redirected to the actual malicious lawmaking by the leap at the terminate. This technique requires the attacker to guess where on the stack the NOP-sled is instead of the comparatively small-scale shellcode.[7]
Because of the popularity of this technique, many vendors of intrusion prevention systems will search for this design of no-op machine instructions in an endeavor to detect shellcode in use. It is important to note that a NOP-sled does non necessarily incorporate only traditional no-op motorcar instructions; any instruction that does not corrupt the car country to a indicate where the shellcode will non run tin can be used in place of the hardware assisted no-op. Equally a result, it has get mutual practice for exploit writers to compose the no-op sled with randomly chosen instructions which will have no real effect on the shellcode execution.[8]
While this method greatly improves the chances that an set on will be successful, it is not without problems. Exploits using this technique however must rely on some amount of luck that they will gauge offsets on the stack that are within the NOP-sled region.[9] An incorrect guess volition usually outcome in the target program crashing and could alert the system administrator to the aggressor'southward activities. Some other problem is that the NOP-sled requires a much larger amount of memory in which to hold a NOP-sled large plenty to exist of whatever utilise. This can be a problem when the allocated size of the affected buffer is besides pocket-sized and the current depth of the stack is shallow (i.e., there is not much space from the end of the current stack frame to the start of the stack). Despite its problems, the NOP-sled is often the only method that will work for a given platform, environment, or state of affairs, and equally such information technology is still an important technique.
The jump to address stored in a register technique [edit]
The "spring to annals" technique allows for reliable exploitation of stack buffer overflows without the need for extra room for a NOP-sled and without having to guess stack offsets. The strategy is to overwrite the return pointer with something that will cause the program to spring to a known arrow stored within a register which points to the controlled buffer and thus the shellcode. For example, if register A contains a pointer to the offset of a buffer so any jump or call taking that register every bit an operand can be used to proceeds command of the flow of execution.[ten]

An instruction from ntdll.dll to telephone call the DbgPrint() routine contains the i386 machine opcode for jmp esp.
In practice a plan may not intentionally contain instructions to jump to a item register. The traditional solution is to find an unintentional instance of a suitable opcode at a fixed location somewhere inside the program memory. In effigy Eastward on the left is an case of such an unintentional instance of the i386 jmp esp didactics. The opcode for this education is FF E4.[11] This two-byte sequence can exist constitute at a i-byte offset from the starting time of the instruction call DbgPrint at address 0x7C941EED. If an attacker overwrites the program return address with this accost the program will first jump to 0x7C941EED, interpret the opcode FF E4 every bit the jmp esp instruction, and will so jump to the top of the stack and execute the attacker's code.[12]
When this technique is possible the severity of the vulnerability increases considerably. This is considering exploitation will work reliably enough to automate an attack with a virtual guarantee of success when it is run. For this reason, this is the technique virtually commonly used in Net worms that exploit stack buffer overflow vulnerabilities.[13]
This method also allows shellcode to be placed after the overwritten return address on the Windows platform. Since executables are mostly based at address 0x00400000 and x86 is a Niggling Endian architecture, the last byte of the return address must exist a null, which terminates the buffer re-create and zip is written beyond that. This limits the size of the shellcode to the size of the buffer, which may be overly restrictive. DLLs are located in loftier memory (above 0x01000000) and and so have addresses containing no cypher bytes, so this method tin can remove zippo bytes (or other disallowed characters) from the overwritten return accost. Used in this way, the method is often referred to as "DLL trampolining".
Protective countermeasures [edit]
Various techniques have been used to detect or prevent buffer overflows, with diverse tradeoffs. The most reliable way to avoid or prevent buffer overflows is to use automated protection at the linguistic communication level. This sort of protection, however, cannot be applied to legacy code, and often technical, concern, or cultural constraints call for a vulnerable language. The following sections describe the choices and implementations bachelor.
Choice of programming language [edit]
Assembly and C/C++ are popular programming languages that are vulnerable to buffer overflow, in role because they permit direct access to memory and are non strongly typed.[14] C provides no born protection against accessing or overwriting data in whatever part of retentivity; more than specifically, it does not check that data written to a buffer is inside the boundaries of that buffer. The standard C++ libraries provide many ways of safely buffering data, and C++'s Standard Template Library (STL) provides containers that can optionally perform premises checking if the programmer explicitly calls for checks while accessing data. For instance, a vector'due south member role at() performs a premises check and throws an out_of_range exception if the bounds bank check fails.[15] However, C++ behaves just like C if the premises cheque is not explicitly called. Techniques to avoid buffer overflows also exist for C.
Languages that are strongly typed and do not allow direct retentivity access, such as COBOL, Coffee, Python, and others, prevent buffer overflow from occurring in nearly cases.[14] Many programming languages other than C/C++ provide runtime checking and in some cases even compile-time checking which might transport a alarm or raise an exception when C or C++ would overwrite data and continue to execute further instructions until erroneous results are obtained which might or might not cause the program to crash. Examples of such languages include Ada, Eiffel, Lisp, Modula-2, Smalltalk, OCaml and such C-derivatives as Cyclone, Rust and D. The Coffee and .Internet Framework bytecode environments likewise require premises checking on all arrays. About every interpreted language will protect against buffer overflows, signaling a well-defined fault status. Often where a language provides enough blazon information to do bounds checking an option is provided to enable or disable information technology. Static lawmaking assay tin can remove many dynamic bound and type checks, just poor implementations and bad-mannered cases tin significantly decrease performance. Software engineers must advisedly consider the tradeoffs of safety versus functioning costs when deciding which language and compiler setting to use.
Use of safe libraries [edit]
The problem of buffer overflows is common in the C and C++ languages because they expose low level representational details of buffers equally containers for data types. Buffer overflows must thus be avoided by maintaining a loftier degree of correctness in code which performs buffer management. It has also long been recommended to avoid standard library functions which are not bounds checked, such as gets, scanf and strcpy. The Morris worm exploited a gets call in fingerd.[xvi]
Well-written and tested abstract information type libraries which centralize and automatically perform buffer management, including premises checking, can reduce the occurrence and impact of buffer overflows. The two main building-block data types in these languages in which buffer overflows normally occur are strings and arrays; thus, libraries preventing buffer overflows in these data types can provide the vast majority of the necessary coverage. Withal, failure to use these prophylactic libraries correctly can outcome in buffer overflows and other vulnerabilities; and naturally, any bug in the library itself is a potential vulnerability. "Safe" library implementations include "The Better Cord Library",[17] Vstr[18] and Erwin.[xix] The OpenBSD operating system's C library provides the strlcpy and strlcat functions, simply these are more limited than total safe library implementations.
In September 2007, Technical Report 24731, prepared past the C standards committee, was published;[20] it specifies a set of functions which are based on the standard C library's string and I/O functions, with boosted buffer-size parameters. Even so, the efficacy of these functions for the purpose of reducing buffer overflows is disputable; it requires programmer intervention on a per function phone call basis that is equivalent to intervention that could make the analogous older standard library functions buffer overflow safe.[21]
Buffer overflow protection [edit]
Buffer overflow protection is used to find the most mutual buffer overflows by checking that the stack has not been altered when a function returns. If it has been altered, the program exits with a partitioning fault. Three such systems are Libsafe,[22] and the StackGuard [23] and ProPolice [24] gcc patches.
Microsoft's implementation of Data Execution Prevention (DEP) way explicitly protects the pointer to the Structured Exception Handler (SEH) from being overwritten.[25]
Stronger stack protection is possible by splitting the stack in two: 1 for data and ane for role returns. This split is present in the Forth language, though it was not a security-based blueprint conclusion. Regardless, this is not a complete solution to buffer overflows, equally sensitive data other than the return address may all the same be overwritten.
Arrow protection [edit]
Buffer overflows work by manipulating pointers, including stored addresses. PointGuard was proposed as a compiler-extension to prevent attackers from being able to reliably manipulate pointers and addresses.[26] The approach works past having the compiler add code to automatically XOR-encode pointers before and after they are used. Theoretically, considering the attacker does not know what value will be used to encode/decode the pointer, he cannot predict what information technology will point to if he overwrites information technology with a new value. PointGuard was never released, but Microsoft implemented a similar approach get-go in Windows XP SP2 and Windows Server 2003 SP1.[27] Rather than implement pointer protection as an automatic feature, Microsoft added an API routine that can be chosen. This allows for amend performance (because it is non used all of the time), but places the burden on the developer to know when it is necessary.
Considering XOR is linear, an attacker may exist able to manipulate an encoded pointer past overwriting just the lower bytes of an accost. This can allow an attack to succeed if the assailant is able to attempt the exploit multiple times or is able to complete an assault by causing a pointer to bespeak to one of several locations (such as any location within a NOP sled).[28] Microsoft added a random rotation to their encoding scheme to address this weakness to partial overwrites.[29]
Executable space protection [edit]
Executable infinite protection is an approach to buffer overflow protection which prevents execution of code on the stack or the heap. An aggressor may use buffer overflows to insert arbitrary code into the memory of a programme, simply with executable infinite protection, any attempt to execute that code will crusade an exception.
Some CPUs support a feature called NX ("No eXecute") or XD ("eXecute Disabled") bit, which in conjunction with software, can be used to mark pages of data (such equally those containing the stack and the heap) as readable and writable but not executable.
Some Unix operating systems (e.grand. OpenBSD, macOS) transport with executable space protection (e.g. W^X). Some optional packages include:
- PaX[30]
- Exec Shield[31]
- Openwall[32]
Newer variants of Microsoft Windows too support executable space protection, called Data Execution Prevention.[33] Proprietary add together-ons include:
- BufferShield[34]
- StackDefender[35]
Executable space protection does non generally protect against return-to-libc attacks, or any other set on which does not rely on the execution of the attackers code. However, on 64-bit systems using ASLR, every bit described below, executable space protection makes it far more hard to execute such attacks.
Accost infinite layout randomization [edit]
Accost space layout randomization (ASLR) is a figurer security characteristic which involves arranging the positions of central data areas, usually including the base of the executable and position of libraries, heap, and stack, randomly in a process' accost infinite.
Randomization of the virtual memory addresses at which functions and variables can exist found tin make exploitation of a buffer overflow more hard, but non impossible. It likewise forces the assailant to tailor the exploitation attempt to the individual arrangement, which foils the attempts of internet worms.[36] A similar but less effective method is to rebase processes and libraries in the virtual accost space.
Deep packet inspection [edit]
The use of deep bundle inspection (DPI) can find, at the network perimeter, very basic remote attempts to exploit buffer overflows by use of attack signatures and heuristics. These are able to block packets which have the signature of a known attack, or if a long serial of No-Operation instructions (known as a NOP-sled) is detected, these were once used when the location of the exploit'due south payload is slightly variable.
Parcel scanning is non an effective method since it can only forbid known attacks and there are many means that a NOP-sled tin can be encoded. Shellcode used by attackers tin can be made alphanumeric, metamorphic, or cocky-modifying to evade detection by heuristic packet scanners and intrusion detection systems.
Testing [edit]
Checking for buffer overflows and patching the bugs that cause them naturally helps prevent buffer overflows. One common automated technique for discovering them is fuzzing.[37] Edge case testing tin can as well uncover buffer overflows, as can static analysis.[38] Once a potential buffer overflow is detected, it must be patched; this makes the testing arroyo useful for software that is in evolution, just less useful for legacy software that is no longer maintained or supported.
History [edit]
Buffer overflows were understood and partially publicly documented every bit early as 1972, when the Computer Security Technology Planning Written report laid out the technique: "The code performing this function does non check the source and destination addresses properly, permitting portions of the monitor to be overlaid by the user. This tin be used to inject code into the monitor that will permit the user to seize control of the automobile."[39] Today, the monitor would exist referred to as the kernel.
The earliest documented hostile exploitation of a buffer overflow was in 1988. It was one of several exploits used by the Morris worm to propagate itself over the Net. The program exploited was a service on Unix chosen finger.[40] Later, in 1995, Thomas Lopatic independently rediscovered the buffer overflow and published his findings on the Bugtraq security mailing list.[41] A year later on, in 1996, Elias Levy (likewise known every bit Aleph One) published in Phrack mag the paper "Corking the Stack for Fun and Turn a profit",[42] a pace-by-footstep introduction to exploiting stack-based buffer overflow vulnerabilities.
Since so, at least ii major internet worms have exploited buffer overflows to compromise a large number of systems. In 2001, the Code Ruby-red worm exploited a buffer overflow in Microsoft'due south Net Information Services (IIS) 5.0[43] and in 2003 the SQL Slammer worm compromised machines running Microsoft SQL Server 2000.[44]
In 2003, buffer overflows nowadays in licensed Xbox games take been exploited to let unlicensed software, including homebrew games, to run on the console without the need for hardware modifications, known as modchips.[45] The PS2 Independence Exploit also used a buffer overflow to attain the aforementioned for the PlayStation 2. The Twilight hack accomplished the same with the Wii, using a buffer overflow in The Legend of Zelda: Twilight Princess.
Meet also [edit]
- Billion laughs
- Buffer over-read
- Coding conventions
- Calculator security
- End-of-file
- Heap overflow
- Ping of decease
- Port scanner
- Return-to-libc attack
- Condom-critical arrangement
- Security-focused operating arrangement
- Self-modifying lawmaking
- Software quality
- Shellcode
- Stack buffer overflow
- Uncontrolled format string
References [edit]
- ^ "CORE-2007-0219: OpenBSD'southward IPv6 mbufs remote kernel buffer overflow". Retrieved 2007-05-xv .
- ^ "Modern Overflow Targets" (PDF) . Retrieved 2013-07-05 .
- ^ "The Metasploit Opcode Database". Archived from the original on 12 May 2007. Retrieved 2007-05-xv .
- ^ "Microsoft Technet Security Bulletin MS04-028". Microsoft. Archived from the original on 2011-08-04. Retrieved 2007-05-xv .
- ^ "Creating Capricious Shellcode In Unicode Expanded Strings" (PDF). Archived from the original (PDF) on 2006-01-05. Retrieved 2007-05-15 .
- ^ Vangelis (2004-12-08). "Stack-based Overflow Exploit: Introduction to Classical and Advanced Overflow Technique". Wowhacker via Neworder. Archived from the original (text) on August 18, 2007.
- ^ Balaban, Murat. "Buffer Overflows Demystified" (text). Enderunix.org.
- ^ Akritidis, P.; Evangelos P. Markatos; Thousand. Polychronakis; Kostas D. Anagnostakis (2005). "STRIDE: Polymorphic Sled Detection through Instruction Sequence Assay." (PDF). Proceedings of the 20th IFIP International Information Security Conference (IFIP/SEC 2005). IFIP International Information Security Conference. Archived from the original (PDF) on 2012-09-01. Retrieved 2012-03-04 .
- ^ Klein, Christian (September 2004). "Buffer Overflow" (PDF). Archived from the original (PDF) on 2007-09-28.
- ^ Shah, Saumil (2006). "Writing Metasploit Plugins: from vulnerability to exploit" (PDF). Hack In The Box. Kuala Lumpur. Retrieved 2012-03-04 .
- ^ Intel 64 and IA-32 Architectures Software Developer's Manual Volume 2A: Pedagogy Set Reference, A-M (PDF). Intel Corporation. May 2007. pp. iii–508. Archived from the original (PDF) on 2007-eleven-29.
- ^ Alvarez, Sergio (2004-09-05). "Win32 Stack BufferOverFlow Real Life Vuln-Dev Process" (PDF). It Security Consulting. Retrieved 2012-03-04 .
- ^ Ukai, Yuji; Soeder, Derek; Permeh, Ryan (2004). "Surround Dependencies in Windows Exploitation". BlackHat Japan. Japan: eEye Digital Security. Retrieved 2012-03-04 .
- ^ a b https://world wide web.owasp.org/index.php/Buffer_OverflowsBuffer Overflows article on OWASP Archived 2016-08-29 at the Wayback Auto
- ^ "vector::at - C++ Reference". Cplusplus.com. Retrieved 2014-03-27 .
- ^ http://wiretap.expanse.com/Gopher/Library/Techdoc/Virus/inetvir.823 [ permanent expressionless link ]
- ^ "The Better Cord Library".
- ^ "The Vstr Homepage". Archived from the original on 2017-03-05. Retrieved 2007-05-15 .
- ^ "The Erwin Homepage". Retrieved 2007-05-xv .
- ^ International System for Standardization (2007). "Information applied science – Programming languages, their environments and system software interfaces – Extensions to the C library – Part 1: Premises-checking interfaces". ISO Online Browsing Platform.
- ^ "CERT Secure Coding Initiative". Retrieved 2007-07-30 . [ permanent dead link ]
- ^ "Libsafe at FSF.org". Retrieved 2007-05-20 .
- ^ "StackGuard: Automatic Adaptive Detection and Prevention of Buffer-Overflow Attacks by Cowan et al" (PDF) . Retrieved 2007-05-twenty .
- ^ "ProPolice at X.ORG". Archived from the original on 12 February 2007. Retrieved 2007-05-20 .
- ^ "Bypassing Windows Hardware-enforced Data Execution Prevention". Archived from the original on 2007-04-30. Retrieved 2007-05-twenty .
- ^ "12th USENIX Security Symposium – Technical Newspaper". www.usenix.org . Retrieved 3 April 2018.
- ^ "Protecting against Pointer Subterfuge (Kinda!)". msdn.com. Archived from the original on 2010-05-02. Retrieved 3 Apr 2018.
- ^ "USENIX - The Advanced Computing Systems Association" (PDF). www.usenix.org . Retrieved 3 April 2018.
- ^ "Protecting against Pointer Subterfuge (Redux)". msdn.com. Archived from the original on 2009-12-19. Retrieved iii April 2018.
- ^ "PaX: Homepage of the PaX squad". Retrieved 2007-06-03 .
- ^ "KernelTrap.Org". Archived from the original on 2012-05-29. Retrieved 2007-06-03 .
- ^ "Openwall Linux kernel patch ii.four.34-ow1". Archived from the original on 2012-02-19. Retrieved 2007-06-03 .
- ^ "Microsoft Technet: Data Execution Prevention". Archived from the original on 2006-06-22. Retrieved 2006-06-xxx .
- ^ "BufferShield: Prevention of Buffer Overflow Exploitation for Windows". Retrieved 2007-06-03 .
- ^ "NGSec Stack Defender". Archived from the original on 2007-05-xiii. Retrieved 2007-06-03 .
- ^ "PaX at GRSecurity.net". Retrieved 2007-06-03 .
- ^ "The Exploitant - Security info and tutorials". Retrieved 2009-eleven-29 .
- ^ Larochelle, David; Evans, David (13 August 2001). "Statically Detecting Likely Buffer Overflow Vulnerabilities". USENIX Security Symposium. 32.
- ^ "Computer Security Engineering Planning Study" (PDF). p. 61. Archived from the original (PDF) on 2011-07-21. Retrieved 2007-eleven-02 .
- ^ ""A Tour of The Worm" by Donn Seeley, Academy of Utah". Archived from the original on 2007-05-20. Retrieved 2007-06-03 .
- ^ "Bugtraq security mailing list archive". Archived from the original on 2007-09-01. Retrieved 2007-06-03 .
- ^ ""Smashing the Stack for Fun and Profit" by Aleph 1". Retrieved 2012-09-05 .
- ^ "eEye Digital Security". Retrieved 2007-06-03 .
- ^ "Microsoft Technet Security Bulletin MS02-039". Microsoft. Archived from the original on 2008-03-07. Retrieved 2007-06-03 .
- ^ "Hacker breaks Xbox protection without mod-chip". Archived from the original on 2007-09-27. Retrieved 2007-06-03 .
External links [edit]
- "Discovering and exploiting a remote buffer overflow vulnerability in an FTP server" by Raykoid666
- "Smashing the Stack for Fun and Turn a profit" by Aleph One
- Gerg, Isaac (2005-05-02). "An Overview and Example of the Buffer-Overflow Exploit" (PDF). IAnewsletter. Information Assurance Technology Assay Center. seven (4): 16–21. Archived from the original (PDF) on 2006-09-27. Retrieved 2019-03-17 .
- CERT Secure Coding Standards
- CERT Secure Coding Initiative
- Secure Coding in C and C++
- SANS: inside the buffer overflow attack
- "Advances in side by side retentiveness overflows" past Nomenumbra
- A Comparison of Buffer Overflow Prevention Implementations and Weaknesses
- More than Security Whitepapers about Buffer Overflows
- Affiliate 12: Writing Exploits III from Sockets, Shellcode, Porting & Coding: Reverse Engineering Exploits and Tool Coding for Security Professionals past James C. Foster (ISBN 1-59749-005-9). Detailed explanation of how to utilise Metasploit to develop a buffer overflow exploit from scratch.
- Computer Security Engineering science Planning Study, James P. Anderson, ESD-TR-73-51, ESD/AFSC, Hanscom AFB, Bedford, MA 01731 (Oct 1972) [NTIS Advertizement-758 206]
- "Buffer Overflows: Anatomy of an Exploit" by Nevermore
- Secure Programming with GCC and GLibc Archived 2008-eleven-21 at the Wayback Machine (2008), by Marcel Holtmann
- "Criação de Exploits com Buffer Overflor – Parte 0 – Um pouco de teoria " (2018), by Helvio Junior (M4v3r1ck)
What Type Of Attack Exploits A Lack Of Bounds Checking On The Size Of Data Stored In An Array?,
Source: https://en.wikipedia.org/wiki/Buffer_overflow
Posted by: sokolmilise.blogspot.com


0 Response to "What Type Of Attack Exploits A Lack Of Bounds Checking On The Size Of Data Stored In An Array?"
Post a Comment